In the beginning of 2022, I attended the “VMware Cloud Director: Advanced Networking with NSX-T Data Center” training for VCD 10.2. The training touched on a couple of topics, that are blog worthy. Let’s start with the next one in this latest Cloud Director series. Other posts in this series are:
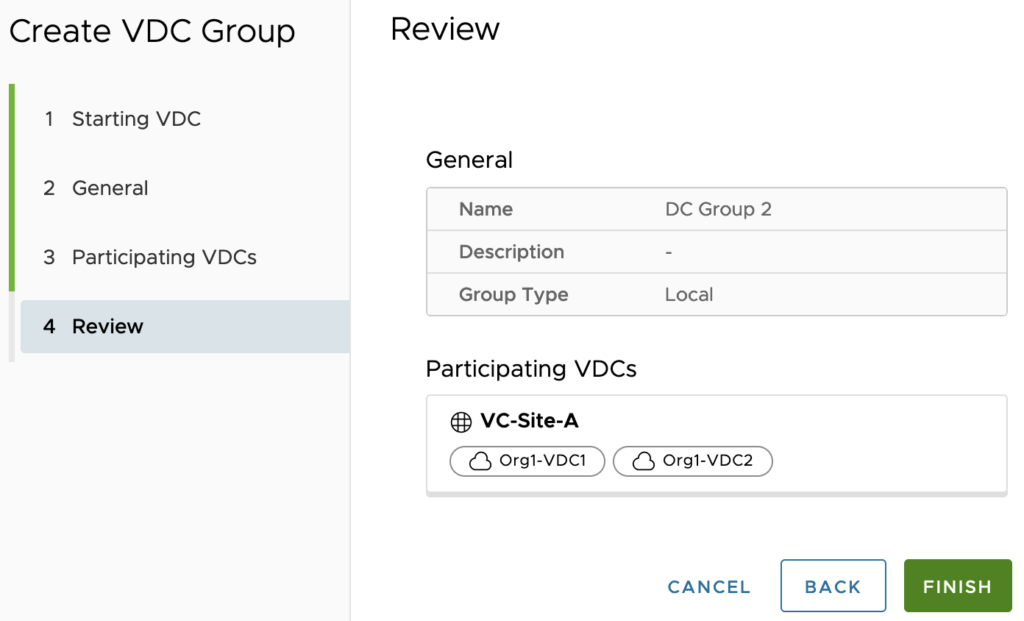
Since Cloud Director (VCD) 10.2, one or more NSX-T backed Virtual Datacenters (VDC’s) belonging to the same tenant can be grouped together in so called Data Center Groups (DCG) up to a maximum of 16 VDC’s in single DCG. It’s primary function is to provide cross-VDC network features, like:
- Centralized networking administration
- Centralized egress point
- East-west traffic between VDC’s in the Data Center Group
- Distributed firewalling (DFW) applied across a Data Center Group
Data Center Groups use-cases
This relatively new DCG features is an awesome way for cross-VDC networking and security, instead of using much more limited “Shared” feature before. The “Shared” network feature for example could not be used for distributed firewalling, which is possible now with DCG.
Imagine a VDC that is replicated to a destination VDC in a DR site, which has the same firewall rules applied without reconfiguration. Or an Edge gateway attached to a VDC can be used by all of them. Very powerful.
Comparing features
Cloud Director networking features can be either added to a single VDC or a DC Group, but not both. Some features are available depending in one or the other. Let’s check it out by putting it into a table for visibility.
| Features | Virtual Data Center (VDC) | Data Center Group (DCG) |
| Networking | ||
| Organization VDC Network: Routed | Yes | Yes |
| Organization VDC Network: Isolated | Yes | Yes |
| Organization VDC Network: Direct (Can be added to multiple VDCs, cross Orgs) | Yes (Shareable) | No |
| -External Network: Distributed Port Groups | ✓ | – |
| -External Network: Standard Port Groups | ✓ | – |
| -External Network: NSX-T Segment | ✓ | – |
| Organization VDC Network: Imported (Can be added to single VDC) | Yes | Partial |
| -Imported Network: NSX-T Segment | ✓ | ✓ |
| -Imported Network: Distributed Port Groups | ✓ (Shareable) | – |
| Security | ||
| Distributed Firewall | No | Yes |
| Edge Firewall | Yes | Yes |
| Dynamic Groups | No | Yes |
| Static Groups | Yes | Yes |
| IP Sets | Yes | Yes |
The table above directly shows that all distributed and therefore dynamic groups are only available in a DCG. Secondly it shows that “Shared” and Direct connected Org VDC networks are only possible in a VDC.
Direct or Imported networks?
The most important difference between Direct and Imported network is the intended use. The main difference is that Direct connected networks can be added to one or more VDC’s belonging to different Orgs, but not to a DCG. An Imported network can be added to a single VDC or DCG.
Prerequisites for Data Center Groups
When using future Data Center Groups nowadays it needs NSX-T backed pVDCs and a set of Compute and Networks scopes. Compute scope at least need to be set on the vCenter object in VCD to define regions and can be overridden on pVDC level to define availability zones within that region.
On the networking part, a Network scope needs to be set on the NSX-T Manager object in VCD to define the regional or even inter-regional scope of the Manager.
Let’s summarize requirements:
- A NSX-T backed Provider VDC (pVDC)
- A configured Compute Provider Scope
- Can be viewed as a region
- Compute Provider Scope is primarily set on vCenter object within VCD
- VCD UI: Resources > Infrastructure Resources > vCenter Server Instances > “<vCenter Name>” > General > vCenter Info > Compute Provider Scope
- Compute Provider Scope can be overridden on pVDC
- Can be viewed as a availability zone with in a region
- VCD UI: Resources > Cloud Resources > pVDC > “<pVDC Name>” > Configure > General > Compute Provider Scope
- If Compute Provider Scope is deleted on pVDC, the parent vCenter “Compute Provider Scope” is used after performing a manual “Sync” in the DCG scope.
- A configured Network Provider Scope
- Can often be viewed as inter-region scope
- Network Provider Scope is set on NSX-T Manager within VCD
- VCD UI: Resources > Infrastructure Resources > NSX-T > NSX-T Managers > “<NSX-T Manager Name>” > General > Network Provider Scope
The result of the above can be seen below.
To conclude
DCG is a very powerful feature of VCD 10.2+ and combined with NSX-T backed pVDC, it can contribute to lots of single and multi-site use-cases. For example:
- Centralized networking administration
- Centralized egress point
- East-west traffic between VDC’s in the Data Center Group
- Distributed firewalling (DFW) applied across a Data Center Group
When multi-site is needed, this currently only works with a single NSX-T Manager instance managing multiple sites, so called multi-site lite. The NSX-T federation feature is not supported at the time.
Useful links
New Networking Features in VMware Cloud Director 10.2
Managing Data Center Group Networking with NSX-T Data Center



0 Comments